This post will explain how to recover ifla files. The Ifla ransomware most likely spreads to PCs through malicious file attachments or piracy websites that allow the distribution of malware-laced packages. Because these penetration tactics allow for stealthy dissemination, the user simply notices the file identifier.
The ransom note _readme.txt appears on the screen and in folders with locked data once the data has been encrypted. The demand for payment would seem acceptable given that ransomware victims get a 50% discount for the first 72 hours after infection.
However, it is never a good idea to approach these thieves or consider offering them money. This bitcoin transfer could result in more malware infection, data and money loss, or both. Remove the infection instead of paying or using hasty data recovery services from questionable sources.
How To Recover Ifla Files? 2022 Guide
In this article, you can know about How To Recover Ifla Files? 2022 Guide here are the details below;
Remove the ransomware
The removal of this Ifla file infection could be difficult because of the persistence offered by the other components that run on the computer. Background processes and even other viruses may start risky procedures and seriously damage the computer since trojans or other cyber dangers can be easily used as vectors for infection and subsequent ransomware propagation.
For the cleansing procedure, antivirus programmes that can locate ransomware files and other linked software or online dangers are essential. A thorough system scan ensures that every malware is found and can be immediately removed without putting the computer at risk.
Notably, eliminating the Ifla ransomware is a necessary step for optimum system efficiency; nevertheless, this is different from virus decryption or file recovery. More threat components could disrupt other processes and start the machine’s second round of file locking, thus removal is necessary. Remove the virus as soon as you see that these common files have been encoded.
Decrypt affected files
The Djvu ransomware family cannot currently be decoded. It used to be because the primary method of file locking used by developers was offline keys. This ID is generated when the version is developed and released into the wild. Since a connection to servers and online domains is not required in this scenario, one recovered decryption key can aid further victims in restoring corrupted files.
The application below is creating this method, which can help many users recover their files. The most recent versions, like this Ifla ransomware, are more difficult to decode. Versions released after August 2019 mostly employ online keys that are generated during each distinct encryption process and may be connected to the particular device. In the event that the connection to the C&C server is lost, offline keys are still used. Check to see whether you can recover your data.
To get the app, go to the Emsisoft official website.
When STOPDjvu.exe manifests, click on it.
Follow the on-screen instructions.
The application need to be able to locate the affected folders.
You can also do that by selecting Add folder.
There are specific outcomes that can show whether the decryption is doable.
Restore damaged system components
Ransomware can lock frequently used files, however further issues are created with the system data and harm to such folders. A virus like the Ifla file infection has the power to alter system settings, preferences, and other settings directly.
DLL files and other components in system folders may be harmed while keeping the machine running the necessary processes. You must fix the corrupted files in order to increase performance once more. This can be used to restore some of the system properties needed for file recovery.
- Install Reimage.
- Run a complete system scan and wait for the analysis’s findings.
- Follow the instructions on the screen.
- Allow the gadget to be looked at.
- Review the Summary.
- You can manually resolve issues from the list.
- Buying a licenced version can help with fixing important issues.
Recover the locked files.
- Purchase a product from a reputable seller, such as Data Recovery Pro.
- Follow the installation instructions.
- Once you’ve finished, use the application.
- Select particular folders or the All option to restore.
- Choose Next.
- Turn on the Deep scan at the base.
- Decide the disc you want to have scanned.
- To recover the data after the scan is finished, click Recover.
FAQs
What is the Ifla virus?
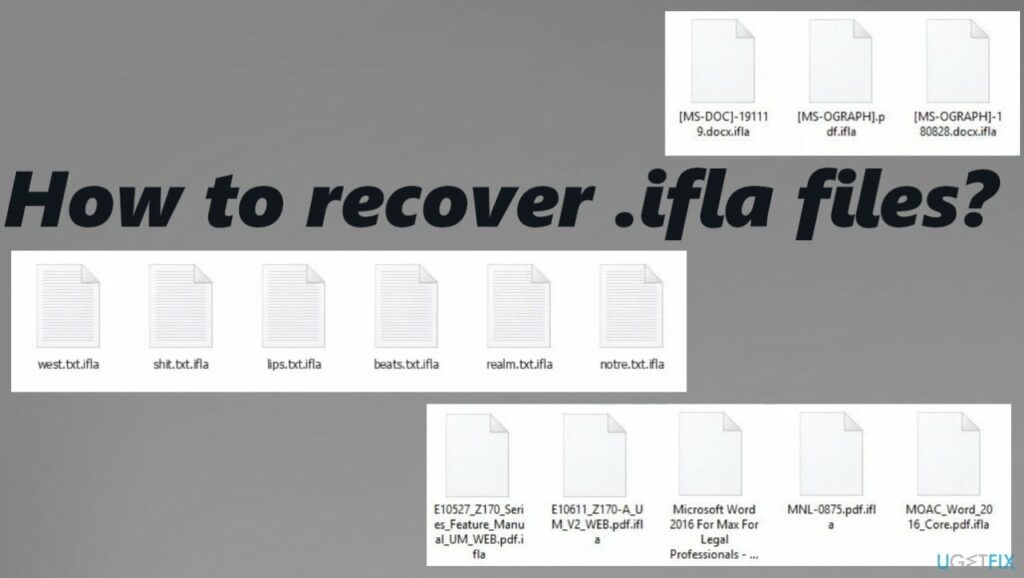
The Ifla virus is a brand-new ransomware from the STOP ransomware family (Djvu). Ransomware is a sort of malware that encrypts the victim’s files and demands money to decrypt them. Ifla virus creates files with the name “_readme.txt” that contain the ransom demand message in addition to encrypting them and renaming them with the.ifla suffix. For instance, a file named “image.jpg” will become “image.jpg.ifla,” “document.docx” will become “document.docx.ifla,” “invoice.pdf.ifla,” and so forth.
How can I recover dfwe-locked files?
- Remove the encryption from the data.
- Eliminate the computer malware ransomware.
- Recover the system’s corrupted data.
- Recoup data from damaged files.
- For online privacy protection, use a VPN client.
- Data recovery tools can halt irreversible file loss.
How can I get the CRYPT14 file back?
You can do this by manually restoring your message history by changing your most recent CRYPT14 file to msgstore.database.crypt14, uninstalling and then reinstalling WhatsApp, and then following the on-screen instructions. For more detailed WhatsApp instructions, click here.