The deep web is the web’s secret world. It is not difficult to gain access to it, but you must take some basic precautions to protect your privacy. The dark web browser (or deep web) is an ostensibly hidden realm that is a long cry from the internet we’ve come to know, love, and expect.
For some, it’s a place of mystery, while for others, it’s a place of awe. While you may have preconceived notions about what the dark web browser is like, the networks do have advantages. While you’ve definitely heard about all of the illicit behavior that goes on, one of the most compelling reasons for using a Dark Web browser is the ability to surf the internet anonymously.
If you still have questions, we previously posted a blog about the deep/Dark Web browser, detailing what it is, why it is essential, and how to access it you can read it here. We’ll expand on one aspect of the previous blog-the anonymity of a Dark Web browser– in this post.
When browsing the Dark Web browser, it is critical to leave no trace, and in order to do so, you will need a good web browser that masks your network traffic and renders you invisible. Well, almost invisible, because you’ll need a VPN to finish the job. The following is a list of the top ten Deep/Dark Web browsers. You can use any of these to surf the web safely and anonymously.
Best Deep/Dark Web Browser
You’ll need a Dark Web browser that can connect to the entry and exit nodes to connect to the Dark/Deep Web and Tor Network. We’ve compiled a list of eight of the top Deep/Dark Web browser to help you find the hidden web browser that’s appropriate for you.
ZeroNet
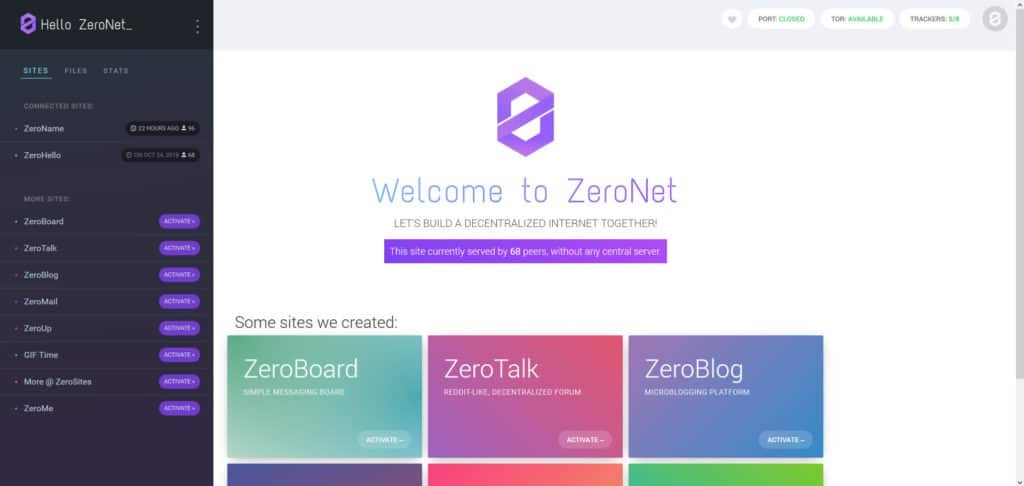
This is decentralized peer-to-peer communication tool is ZeroNet. It makes use of the BitTorrent network and Bitcoin cryptography. It can be used to share files and create web pages. Sites are recognized by a public key rather than an IP address.
It is not a completely anonymous networking platform, but it does support connections to the Tor Network, as do many others — but this may slow it down. Last but not least, Zeronet can be used without an internet connection. We attempted to provide you with a better understanding of what an excellent deep/dark web browser is like. It may be challenging to choose one among a plethora of web browsers if you are just getting started with the deep/dark web.
Tails

Tails stand out among the other deep/dark web browsers since it is based on the original Tor Browser. It can be booted from a flash drive without needing to be installed first. It’s for this reason that it’s frequently referred to as a live operating system. Tails will shut down the OS installed on your machine for extra privacy, and it will only restart after you have finished using it. This demonstrates that Tails is independent of the operating system installed on the machine.
Whonix
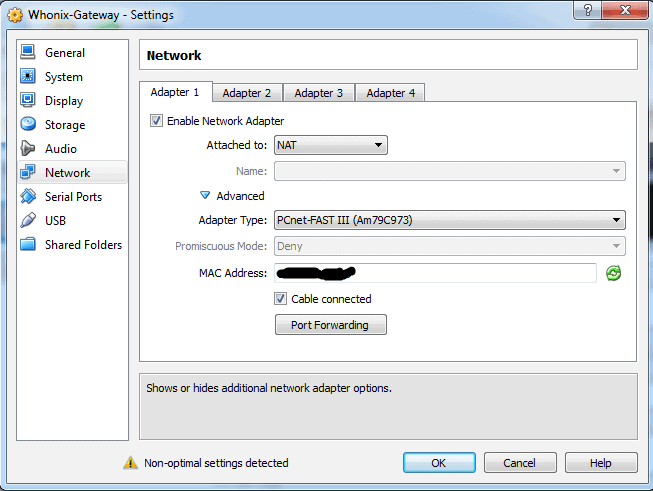
Whonix is a Tor-based Dark Web browser that allows you to surf the web anonymously. It is pre-installed on Qubes and is available for Windows, Mac, and Linux. You can use Qubes-Whonix for enhanced privacy. IP leaks, timing attacks, keystroke deanonymization, and data collection techniques are just a few of the anonymity threats it protects users from.
I2P
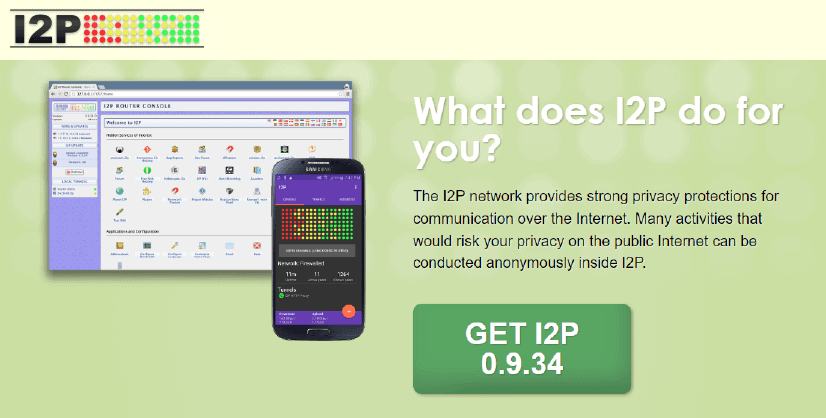
I2P is yet another privacy technique that protects users’ identities. To achieve this, it employs end-to-end encryption. This encryption is done in four layers, and you can use a layered stream to access both the surface and the subsurface. The network is built on messaging and allows for peer-to-peer communication. I2P routes user traffic over around 55000 distributed machines, resulting in a wide variety of possible paths for your messages to travel. This makes it nearly impossible to track down the user.
Waterfox

Waterfox is an open-source Dark Web browser based on Firefox, but it is not affiliated with Mozilla. It does, however, connect to it on a regular basis to safeguard users against harmful add-ons. It’s available in 64-bit versions for Windows, Mac, Linux, and Android mobile devices. Waterfox has a feature that deletes all of your cookies, web browsing history, passwords, and other personal data when you’ve finished surfing.
Freenet
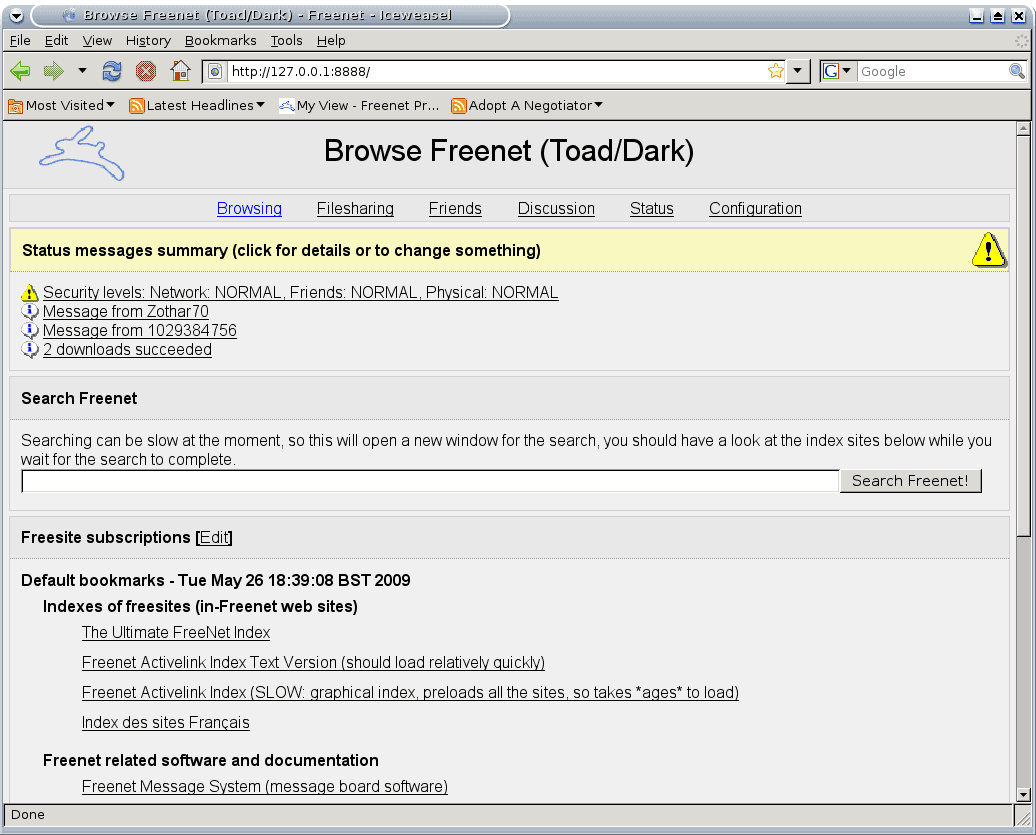
Another peer-to-peer platform that encrypts data before sharing it is Freenet. It employs a system similar to that of other browsers in that communication is routed through various nodes. It encrypts data that is shared over a decentralized, dispersed network, which makes it extremely difficult to attack.
Users who connect to Freenet donate some of their bandwidth and hard drive space. They have the option of using the darknet or the opennet. The key difference in darknet mode is that users can only view anything that has been submitted to the Freenet network and not to any other networks. In addition, copyrights are not enforced in Freenet. Copyrighting entails communication surveillance, which means there is no freedom of speech, which is against their laws.
Firefox

You might be thinking, “How come Firefox is utilized for Dark Web browser surfing?” Firefox is an ordinary browser, after all. It turns out that it isn’t entirely right. It’s grouped with Google Chrome, Safari, Opera, and other browsers. (Of course, Opera isn’t really regular, but we’ll get to that later.)
In order to allow anonymous web browsing, Firefox must be routed to connect through Tor Network. You must manually configure proxy access, which is a rather straightforward process. Tor listens on port 9050 by default, so that’s something you’ll want to change in your configuration, and the proxy server you’ll require is 127.0.0.1.
Tor Browser

Every time you search the Dark Web browser for information, you will come across the Tor Browser. It’s the most advanced Deep Web browser, with the highest level of security and anonymity. As a result, it is the most widely used browser. It was originally developed for the US Army to provide more secure communication, but it is now freely available to anybody with a Windows, Mac, or Linux computer, or even an Android mobile device.
GNunet
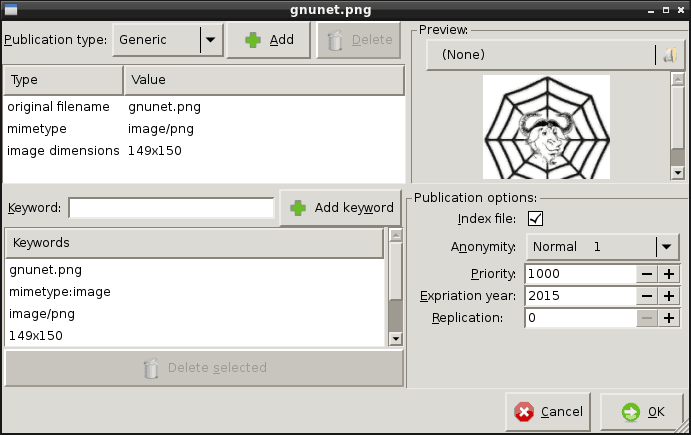
TCP, UDP, HTTP, HTTPS, WLAN, and Bluetooth are all used by GNUnet to offer decentralized, peer-to-peer communication. It informs users which other users they may trust and which they should avoid, safeguarding them from potential threats. It safeguards sensitive data, and one of its key objectives is to minimize the quantity of PII exposed to a minimum.
Subgraph OS
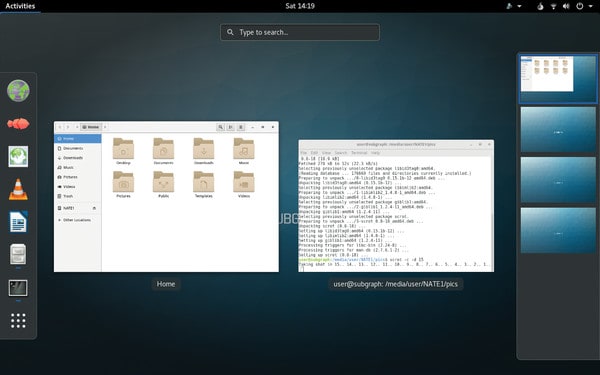
Subgraph is a Tor Dark Web browser-based privacy application that allows you to freely access the web. It also features a Tor integration and uses the same source code. One of its best characteristics is that it is expressly built to protect your OS against adversary attacks – as the website states, “Subgraph OS is an opponent resistant computing platform.” It eliminates malware by utilizing Sandbox containers. Subgraph activates a sandbox container and handles any suspected malware that targets an application.
Conclusion
The Dark Web browser may appear intriguing and even frightening, but several of the. onion websites are actually rather ordinary. There is no compelling reason for normal internet users to visit them because there is already plenty of material available on the surface web. If you do want to have a look, one of the many websites given above is a good place to start. Although the dark web is a very safe and harmless platform, there is always the possibility of encountering anything hazardous or unwelcome.
Keep in mind that the dark web is home to a lot of shady activity, so be cautious and avoid clicking on any links you don’t recognize. Use caution when investigating these and other Dark Web browser connections, and have fun!